Network Devices
Network Devices:
HUB
Hub is one of the basic icons of networking devices which works at physical layer and hence connect networking devices physically together. Hubs are fundamentally used in networks that use twisted pair cabling to connect devices. They are designed to transmit the packets to the other appended devices without altering any of the transmitted packets received. They act as pathways to direct electrical signals to travel along. They transmit the information regardless of the fact if data packet is destined for the device connected or not.
Hub falls in two categories:
Active Hub: They are smarter than the passive hubs. They not only provide the path for the data signals infact they regenerate, concentrate and strengthen the signals before sending them to their destinations. Active hubs are also termed as ‘repeaters’.
Passive Hub: They are more like point contact for the wires to built in the physical network. They have nothing to do with modifying the signals.
Ethernet Hubs
It is a device connecting multiple Ethernet devices together and makes them perform the functions as a single unit. They vary in speed in terms of data transfer rate. Ether utilizes Carrier Sense Multiple Access with Collision Detect (CSMA/CD) to control Media access. Ethernet hub communicates in half-duplex mode where the chances of data collision are inevitable at most of the times.
Switches
Switches are the linkage points of an Ethernet network. Just as in hub, devices in switches are connected to them through twisted pair cabling. But the difference shows up in the manner both the devices; hub and a switch treat the data they receive. Hub works by sending the data to all the ports on the device whereas a switch transfers it only to that port which is connected to the destination device. A switch does so by having an in-built learning of the MAC address of the devices connected to it. Since the transmission of data signals are well defined in a switch hence the network performance is consequently enhanced. Switches operate in full-duplex mode where devices can send and receive data from the switch at the simultaneously unlike in half-duplex mode. The transmission speed in switches is double than in Ethernet hub transferring a 20Mbps connection into 30Mbps and a 200Mbps connection to become 300Mbps. Performance improvements are observed in networking with the extensive usage of switches in the modern days.
The following method will elucidate further how data transmission takes place via switches:
- Cut-through transmission: It allows the packets to be forwarded as soon as they are received. The method is prompt and quick but the possibility of error checking gets overlooked in such kind of packet data transmission.
- Store and forward: In this switching environment the entire packet are received and ‘checked’ before being forwarded ahead. The errors are thus eliminated before being propagated further. The downside of this process is that error checking takes relatively longer time consequently making it a bit slower in processing and delivering.
- Fragment Free: In a fragment free switching environment, a greater part of the packet is examined so that the switch can determine whether the packet has been caught up in a collision. After the collision status is determined, the packet is forwarded.
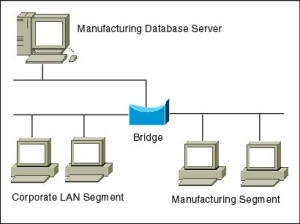
Bridges
A bridge is a computer networking device that builds the connection with the other bridge networks which use the same protocol. It works at the Data Link layer of the OSI Model and connects the different networks together and develops communication between them. It connects two local-area networks; two physical LANs into larger logical LAN or two segments of the same LAN that use the same protocol.
Apart from building up larger networks, bridges are also used to segment larger networks into smaller portions. The bridge does so by placing itself between the two portions of two physical networks and controlling the flow of the data between them. Bridges nominate to forward the data after inspecting into the MAC address of the devices connected to every segment. The forwarding of the data is dependent on the acknowledgement of the fact that the destination address resides on some other interface. It has the capacity to block the incoming flow of data as well. Today Learning bridges have been introduced that build a list of the MAC addresses on the interface by observing the traffic on the network. This is a leap in the development field of manually recording of MAC addresses.
Types of Bridges:
There are mainly three types in which bridges can be characterized:
- Transparent Bridge: As the name signifies, it appears to be transparent for the other devices on the network. The other devices are ignorant of its existence. It only blocks or forwards the data as per the MAC address.
- Source Route Bridge: It derives its name from the fact that the path which packet takes through the network is implanted within the packet. It is mainly used in Token ring networks.
- Translational Bridge: The process of conversion takes place via Translational Bridge. It converts the data format of one networking to another. For instance Token ring to Ethernet and vice versa.
Switches superseding Bridges:
Ethernet switches are seen to be gaining trend as compared to bridges. They are succeeding on the account of provision of logical divisions and segments in the networking field. Infact switches are being referred to as multi-port bridges because of their advanced functionality
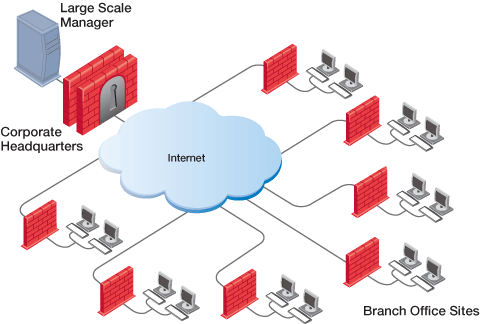
Routers
Routers are network layer devices and are particularly identified as Layer- 3 devices of the OSI Model. They process logical addressing information in the Network header of a packet such as IP Addresses. Router is used to create larger complex networks by complex traffic routing. It has the ability to connect dissimilar LANs on the same protocol. It also has the ability to limit the flow of broadcasts. A router primarily comprises of a hardware device or a system of the computer which has more than one network interface and routing software.
Functionality:
When a router receives the data, it determines the destination address by reading the header of the packet. Once the address is determined, it searches in its routing table to get know how to reach the destination and then forwards the packet to the higher hop on the route. The hop could be the final destination or another router.
Routing tables play a very pivotal role in letting the router makes a decision. Thus a routing table is ought to be updated and complete. The two ways through which a router can receive information are:
- Static Routing: In static routing, the routing information is fed into the routing tables manually. It does not only become a time-taking task but gets prone to errors as well. The manual updating is also required in case of statically configured routers when change in the topology of the network or in the layout takes place. Thus static routing is feasible for tinniest environments with minimum of one or two routers.
- Dynamic Routing: For larger environment dynamic routing proves to be the practical solution. The process involves use of peculiar routing protocols to hold communication. The purpose of these protocols is to enable the other routers to transfer information about to other routers, so that the other routers can build their own routing tables.
Brouters
Brouters are the combination of both the bridge and routers. They take up the functionality of the both networking devices serving as a bridge when forwarding data between networks, and serving as a router when routing data to individual systems. Brouter functions as a filter that allows some data into the local network and redirects unknown data to the other network.
Brouters are rare and their functionality is embedded into the routers functioned to act as bridge as well.
Gateways
Gateway is a device which is used to connect multiple networks and passes packets from one packet to the other network. Acting as the ‘gateway’ between different networking systems or computer programs, a gateway is a device which forms a link between them. It allows the computer programs, either on the same computer or on different computers to share information across the network through protocols. A router is also a gateway, since it interprets data from one network protocol to another.
Others such as bridge converts the data into different forms between two networking systems. Then a software application converts the data from one format into another. Gateway is a viable tool to translate the data format, although the data itself remains unchanged. Gateway might be installed in some other device to add its functionality into another.
Network card
Network cards also known as Network Interface Cards (NICs) are hardware devices that connect a computer with the network. They are installed on the mother board. They are responsible for developing a physical connection between the network and the computer. Computer data is translated into electrical signals send to the network via Network Interface Cards.
They can also manage some important data-conversion function. These days network cards are software configured unlike in olden days when drivers were needed to configure them. Even if the NIC doesn’t come up with the software then the latest drivers or the associated software can be downloaded from the internet as well.
Network protocols
Network protocols define a language of instructions and conventions for communication between the network devices. It is essential that a networked computer must have one or more protocol drivers. Usually, for two computers to interconnect on a network, they must use identical protocols. At times, a computer is designed to use multiple protocols. Network protocols like HTTP, TCP/IP offer a basis on which much of the Internet stands.
System requirement:
- The bus compatibility should be verified on installing an NIC into the system. The commonly used bus system is Peripheral Component Interconnect (PCI)
- Memory I/O addresses and IRQ are needed.
- Need of drivers if not already installed.
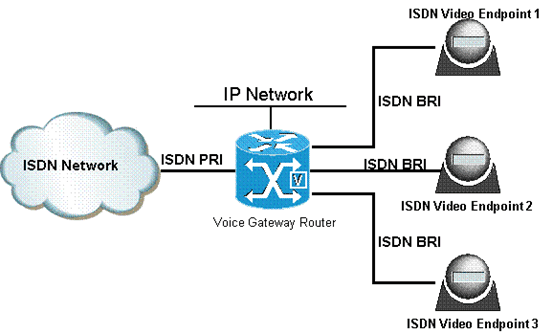
ISDN (Integrated Services Digital Network)
ISDN are used to send over graphic or audio data files. It is a WAN technology that can be used in place of a dial up link. The accessibility of ISDN depends upon the provision of the service by the service provider, the quality of the line set up to your area. It surely provides higher speed than a modem and has the capability to pick up the line and drop it considerably at a faster rate.
ISDN can create numerous communication routes on a single line. Nowadays, even faster and cheaper technologies that ISDN have found their way in the realm of technology.
Modems
Modem is a device which converts the computer-generated digital signals of a computer into analog signals to enable their travelling via phone lines. The ‘modulator-demodulator’ or modem can be used as a dial up for LAN or to connect to an ISP. Modems can be both external, as in the device which connects to the USB or the serial port of a computer, or proprietary devices for handheld gadgets and other devices, as well as internal; in the form of add-in expansion cards for computers and PCMCIA cards for laptops.
Configuration of a modem differs for both the external and internal modem. For internal modems, IRQ – Interrupt request is used to configure the modem along with I/O, which is a memory address. Typically before the installation of built-in modem, integrated serial interfaces are disabled, simultaneously assigning them the COM2 resources.
For external connection of a modem, the modem assigns and uses the resources itself. This is especially useful for the USB port and laptop users as the non-complex and simpler nature of the process renders it far much more beneficial for daily usage.
Upon installation, the second step to ensure the proper working of a modem is the installation of drivers. The modem working speed and processing is dependent on two factors:
- Speed of UART – Universal Asynchronous Receiver or Transmitter chip (installed in the computer to which the modem connection is made)
- Speed of the modem itself
Network Devices Quiz
Quiz 1
Quiz 2
Quiz 3
Quiz 4
Quiz 5
Read more:
- What skills you need to pass CCNA exam
- The Cisco Three Layer Hierarchy Model
- Ethernet Cabling
- Ethernet Networking
- Data Encapsulation
- OSI Layer Model
- Network Topology
- Networking Essentials
- Computer Networking
Free Cisco CCNA Study Guide
Free Practice Tests
- Free MTA Practice Tests and Exams
- Free MCSA Windows 7 Practice Tests and Exams
- Free MCSA Windows 8 Practice Tests and Exams
- Free MCSE and MCSA Windows Server 2012 Practice Tests and Exams
- Free CompTIA A+ Certification Practice Tests and Exams
- A+ Practice Test
- Free CompTIA CDIA+ Certification Practice Tests and Exams
- Free CompTIA Linux+ Certification Practice Tests and Exams
- Free CompTIA Network+ Certification Practice Tests and Exams
- Free CompTIA Project+ Certification Practice Tests and Exams
- Free CompTIA Security+ Certification Practice Tests and Exams
- Free CompTIA Server+ Certification Practice Tests and Exams
- Free CompTIA Storage+ Certification Practice Tests and Exams
- Free CCENT 100-101 ICND1, CCNA 200-101 ICND2, 200-120 CCNA Practice Exams and Tests
- Free Cisco CCNA certification practice tests and Exams Questions
- Free CCNA Security Certification Practice Tests and Exams
- Free CCNA Wireless Certification Practice Tests and Exams
- Free CCNA Voice Certification Practice Tests and Exams
- Free CCNP practice tests and Exams Questions
- Free CCIE Collaboration Certification Practice Tests and Exams
- Free CCIE Routing and Switching Certification Practice Tests and Exams
- Free CCIE Security Certification Practice Tests and Exams
- Free CCIE Wireless 350-050 Practice Exam